Proxy Program For Mac
CCProxy - Windows Proxy Server. CCProxy is easy-to-use and powerful proxy server.CCProxy can support broadband, DSL, dial-up, optical fiber, satellite, ISDN and DDN connections, it helps you build your own proxy server and share Internet connection within the LAN efficiently and easily. CC Proxy Server can act as an HTTP, mail, FTP, SOCKS, news, telnet and HTTPS proxy server. Bypass proxy software for mac free download. Traefik Traefik (pronounced traffic) is a modern HTTP reverse proxy and load balancer that makes deploying m. The X-Proxy app then classifies the proxies into different categories, depending on their security level. Either high anonymous, anonymous or transparent. Overall, X-Proxy is a lightweight solution for browsing anonymously. Its ease of use, coupled with the proxy lists, which it provides, makes it a handy tool for hiding your PC from the web.
How to remove 'Proxy Virus' from Mac?
What is 'Proxy Virus'?
Proxy Virus (also known as MITM Proxy Virus) is a type of browser-hijacking program that has recently become popular. In order to spread this infection, cyber criminals often use various adware-type applications. In most cases, these infiltrate computers without users' permission. Adware is also likely to deliver intrusive advertisements and record information relating to browsing activity.
The initial adware installation process seems normal. After installation, however, users are presented with a deceptive pop-up message encouraging them to update the Safari web browser. After clicking 'OK', users are presented with another pop-up that asks users to enter account credentials. In this way, users might inadvertently grant adware permission to control the Safari browser. Additionally, rogue installers deploy a 'bash script' designed to connect to a remote server and download a .zip archive. The archive is then extracted and a .plist file contained within it is copied to the LaunchDaemons directory. The .plist file contains a reference to another file called 'Titanium.Web.Proxy.Examples.Basic.Standard'. Two additional scripts ('change_proxy.sh' and 'trush_cert.sh') are executed after the next reboot. The 'change_proxy.sh' script is designed to change the system proxy settings, thereby making it use HTTP/S proxy at 'localhost:8003'. The 'trush_cert.sh' script is designed to install a trusted SSL certificate into the keychain. Cyber criminals responsible for this infection use Titanium Web Proxy - an open-source asynchronous HTTP(S) proxy writen in C Sharp (C#). Titanium Web Proxy it is a cross-platform proxy, meaning that it can run on various operating systems, including MacOS. The purpose of this infection is to hijack search engines. Cyber criminals use it to modify Internet search results. Using a proxy to achieve this is rather unusual, since cyber criminals typically employ fake search engines. They use various browser-hijacking applications to modify settings (e.g., new tab URL, default search engine, homepage) by assigning them to certain URLs. Promoted websites often seem normal and their design is usually similar to Bing, Yahoo, Google, and other legitimate search engines. Yet, fake search engines can generate results that lead to malicious websites. Moreover, noticing that such browser settings have been modified is simple because users continually encounter redirects to dubious sites. Using tools such as Proxy Virus is more difficult for these criminals, and yet also more reliable from their point of view. Cyber criminals also deliver fake search results by modifying the content of legitimate search engines. For instance, if a user attempts to search using the Google search engine, the entire website (URL, header, footer, etc.) is genuine, however, the infection modifies the result section. In this way, users are fed with fake results even though they search using legitimate engines. Ultimately, this behavior can lead to further high risk infections - users might inadvertently visit malicious websites. Additionally, cyber criminals use such tactics to increase the traffic of certain websites, which allows them to generate revenue through advertising. The presence of Proxy Virus significantly diminishes the browsing experience and can lead to further computer infections. As mentioned above, adware-type applications are designed to deliver advertisements (e.g., coupons, banners, pop-ups, etc.). These ads might also redirect to malicious websites and even run scripts designed to download/install other unwanted apps. Therefore, clicking them can also lead to installation of infectious apps. Additionally, ads are delivered using tools that enable placement of third party graphical content on any site. Therefore, they often conceal website content, thereby diminishing the browsing experience. Adware-type apps gather information such as IP addresses, website URLs visited, pages viewed, search queries, and other similar details, which are later shared with third parties (potentially, cyber criminals). These people generate revenue by misusing private data. Therefore, information tracking might eventually lead to serious privacy issues, or even identity theft. You are advised to remove all infections, including adware and Proxy Virus.

Proxy Program Mac
| Name | MITM Proxy virus |
| Threat Type | Mac malware, Mac virus, Proxy hijacker, Search hijacker |
| Detection Names (Adobe Flash Player-3.dmg - Fake Adobe Flash Player installer) | Avast (MacOS:Agent-EN [Drp]), BitDefender (Adware.MAC.Bundlore.DMM), Emsisoft (Adware.MAC.Bundlore.DMM (B)), Kaspersky (Not-a-virus:HEUR:AdWare.OSX.Bnodlero.q), Full List (VirusTotal) |
| Symptoms | You see inaccurate search results, your Mac and Internet speed become slower than normal, you see unwanted pop-up ads, you are redirected to dubious websites. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), fake flash player installers, torrent file downloads. |
| Damage | Internet browsing tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites, loss of private information. |
| Malware Removal (Mac) | To eliminate possible malware infections, scan your Mac with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
There are dozens of adware-type applications and browser hijackers online. Typically, these applications offer 'useful features' in attempts to give the impression of legitimacy and trick users to install, however, the only purpose of these applications is to generate revenue for the developers. Rather than giving any real value for regular users, PUAs cause redirects, deliver advertisements, modify settings, and record information.
How did potentially unwanted applications install on my computer?
Adware and browser-hijacking applications are usually proliferated via intrusive advertisements and a deceptive marketing method called 'bundling' - stealth installation of third party applications together with regular (usually free) software. Developers know that users often rush download/installation processes and skip steps. Therefore, 'bundled' apps are usually concealed behind 'Custom/Advanced' settings (or other sections) of these procedures. By carelessly skipping download/installation steps and clicking on advertisements, many users expose their systems to risk of infections and compromise their privacy.
How to avoid installation of potentially unwanted applications?
To prevent this situation, be very cautious when browsing the internet and downloading/installing software. We strongly recommend that you download your software from official sources only, preferably using direct download links. Third party downloaders/installers are typically monetized using the 'bundling' method, and thus such tools should never be used. Do some research before downloading unknown software just to confirm that it is legitimate and virus-free. Intrusive advertisements typically seem legitimate, however, once clicked, they redirect to dubious websites (gambling, adult dating, pornography, and similar). If you continually encounter these ads and redirects, remove all suspicious applications and browser plug-ins immediately. If your computer is already infected with PUAs, we recommend running a scan with Combo Cleaner Antivirus for macOS to automatically eliminate them.
Fake Adobe Flash Player installer promoting Proxy Virus (step 1):
Fake Adobe Flash Player installer promoting Proxy Virus (step 2):
Instant automatic Mac malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of Mac malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner for MacBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Quick menu:
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your 'Applications' folder:
Click the Finder icon. In the Finder window, select 'Applications'. In the applications folder, look for 'MPlayerX','NicePlayer', or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Remove mitm proxy virus related files and folders:
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
Check for adware-generated files in the /Library/LaunchAgents folder:
In the Go to Folder... bar, type: /Library/LaunchAgents
In the “LaunchAgents” folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - “installmac.AppRemoval.plist”, “myppes.download.plist”, “mykotlerino.ltvbit.plist”, “kuklorest.update.plist”, etc. Adware commonly installs several files with the same string.
Check for adware generated files in the /Library/Application Support folder:
In the Go to Folder... bar, type: /Library/Application Support
In the “Application Support” folder, look for any recently-added suspicious folders. For example, “MplayerX” or “NicePlayer”, and move these folders to the Trash.
Check for adware-generated files in the ~/Library/LaunchAgents folder:
In the Go to Folder bar, type: ~/Library/LaunchAgents
In the “LaunchAgents” folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - “installmac.AppRemoval.plist”, “myppes.download.plist”, “mykotlerino.ltvbit.plist”, “kuklorest.update.plist”, etc. Adware commonly installs several files with the same string.
Check for adware-generated files in the /Library/LaunchDaemons folder:
In the Go to Folder... bar, type: /Library/LaunchDaemons
In the “LaunchDaemons” folder, look for recently-added suspicious files. For example “com.aoudad.net-preferences.plist”, “com.myppes.net-preferences.plist”, 'com.kuklorest.net-preferences.plist”, “com.avickUpd.plist”, etc., and move them to the Trash.
Scan your Mac with Combo Cleaner:
If you have followed all the steps in the correct order you Mac should be clean of infections. To be sure your system is not infected run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file double click combocleaner.dmg installer, in the opened window drag and drop Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates it's virus definition database and click 'Start Combo Scan' button.
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays 'no threats found' - this means that you can continue with the removal guide, otherwise it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
MITM Proxy virus removal from Internet browsers:
Remove malicious extensions from Safari:
Remove mitm proxy virus related Safari extensions:
Open Safari browser, from the menu bar, select 'Safari' and click 'Preferences...'.
In the preferences window, select 'Extensions' and look for any recently-installed suspicious extensions. When located, click the 'Uninstall' button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
Remove malicious plug-ins from Mozilla Firefox:
Remove mitm proxy virus related Mozilla Firefox add-ons:
Open your Mozilla Firefox browser. At the top right corner of the screen, click the 'Open Menu' (three horizontal lines) button. From the opened menu, choose 'Add-ons'.
Choose the 'Extensions' tab and look for any recently-installed suspicious add-ons. When located, click the 'Remove' button next to it/them. Note that you can safely uninstall all extensions from your Mozilla Firefox browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Remove malicious extensions from Google Chrome:
Remove mitm proxy virus related Google Chrome add-ons:
Open Google Chrome and click the 'Chrome menu' (three horizontal lines) button located in the top-right corner of the browser window. From the drop-down menu, choose 'More Tools' and select 'Extensions'.
In the 'Extensions' window, look for any recently-installed suspicious add-ons. When located, click the 'Trash' button next to it/them. Note that you can safely uninstall all extensions from your Google Chrome browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
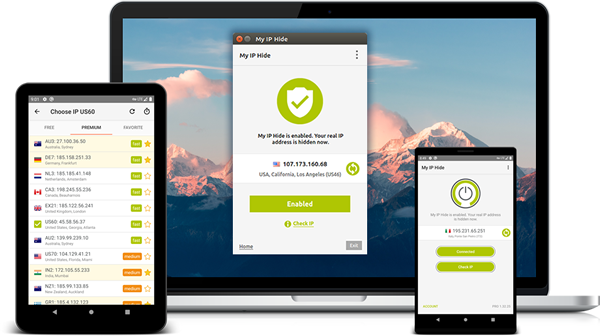
Maintaining privacy on the internet is a cumbersome task. With an enormous network of information stored on various websites, it becomes completely unable to mask the identity of the individual or a company using the data. There comes the use of a proxy server. It works as an intermediate between the client system and the website from which the information is collected. Along with any additional server, a risk of virus and security arises. Since that concern, proxy servers are designed in such a way to ensure safety from any kind of virus attacking the system.a proxy server can be combined with a firewall. It encrypts personal data and retrieves information on safer methods.
Related:
To improve the performance of a specific proxy server the service providers ensured the memory of the search done by the customer in the past. The use of proxy servers is important in case a large network of computers is used. A single proxy server delivers the need of multiple clients and it can be connected to the main server which reduces cost and time for installation.
Smartdnsproxy
This proxy server ensures the use of any restricted website along with safeguarding your system. The service provided by them are secure, and faster than VPN. The service is available for any internet capable device worldwide. You can download unlimited torrents and unlimited device access is ensured. PPTP, L2TP, and open VPN support are the additional feature highlights of the server.
Wingate
This proxy server aims to provide a user friendly approach for businesses. This manages efficiently the time and money to match the necessity of a highly capable web proxy server.
This server ensures the safety of the network by blocking viruses and spam contents. The server can be used in any kind of internet connection.
Efssoft
This is a less complexity server, which helps share internet connection within LAN. Its easy installation enables the user to build the server in less time. The user can access support for unlimited users and groups. Unwanted extra programs are not installed in your system for the ease of working.
Imfirewall
This proxy server is known for its high performance. The server delivers various proxy services like HTTP proxy, SOCKS, SMTP proxy and POP3 proxi. A highly defined user authentication is required for safe installation of the server. The service of this proxy server is free which runs in a windows system.
Echolink
This Echolink server works in such a way that the system is not connected to a central server. It is a peer to peer device. A router and its use of a lot of clients from the single server is not possible by Echolink. To make this possible Echolink proxy server is created. This proxy server can be used in case of high-speed internet connection or a public internet domain like airports, hotels etc.
Ultrasurf
This proxy server provides privacy, security and freedom for its users. It is an anti censorship, pro-privacy software along with protecting the integrity of devices using the server. This software was designed for people in China, where internet activities are highly monitored. The software is recommended to use in internet hotspots and public WIFI.
Gardennetworks
This server provides high internet security by keeping its users IP address hidden. The Gtunnel server address is visible by the destination server, which works as an HTTP or SOCKS proxy server. This server can be used by Linux users. The software is updated automatically. It has a 128 bit data encryption capacity. The server works in Skype enabling peer to peer connection.
Torproject
This server gives importance to personal privacy by defending internet traffic analysis. It is a burden to lose security and being watched by someone. This proxy server enables web browsers, business clients and service persons get rid of network surveillance. It is free and open source server. This server can be used in Windows, Linux/Unix, Android, and Mac.
Hotspotshield
This server provides fast service with security and privacy. The service is available in Windows, Android, Mac, Windows mobile and IOS. The server protects internet connection in public or private networks. Hotspotshield ensures anonymous browsing by encrypting private information. It unblocks censored videos and games quickly.
Betternet
With its 38 million user base, this proxy server enables internet privacy worldwide. The main feature of this server is live streaming websites everywhere without any delay. It helps to bypass any security gateway to access to censored data. A hectic procedure of registration is not needed to use this proxy server.
How to Download a Proxy Server?
A proxy server can be installed in the system by downloading the software needed to run the same, for better performance and privacy for the web searches and downloads. If the use is temporary you can just find an open proxy on the internet. This can support broadband, dial-ups, optical fiber, satellite, ISDN and DDN connections and can build your own proxy server.
Torrent downloads are also supported by proxy servers by hiding the IP address if the user downloading videos. Otherwise, anyone who is using a torrent can see your IP address and it can be an anti-piracy squad.
The risk of identifying a system is still there if you are unable to use an appropriate proxy server. An ideally good server doesn’t keep any user logs which makes it impossible to identify its users. The proxy servers should be analyzed carefully to avoid virus threats and losing any data. Best network security and virus protection servers are mentioned in this article which can be used according to the need.

Proxy Server Mac
Some proxy servers are ideal for an individual purpose, while others for a huge network, some works with all networks while others are restricted to public networks. Proxy servers can be free or chargeable. This also varies with the service it provides. Find a suitable proxy server to enhance the search experience and unlock hidden data and ensure a safe and secure usage of internet.